Google on Thursday welcomed the next instalment of Chrome: the Chrome 25 for Windows, Mac and Linux. The new version includes improvements in managing and securing your extensions, better support for HTML5 time/date inputs, JavaScript Web Speech API support and better WebGL error handling. You can download the latest version directly from google.com/chrome.
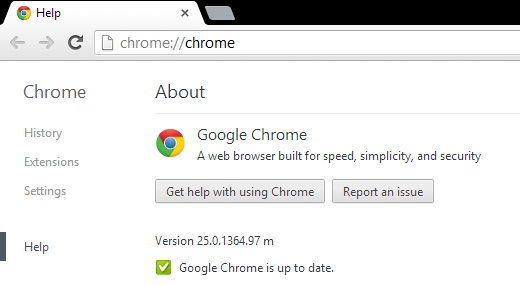
Google Chrome 25
Chrome 25 addresses a total of 22 security holes, nine of which rated as High, eight as Medium and five stands as Low:
- [$1000] [172243] High CVE-2013-0879: Memory corruption with web audio node. Credit to Atte Kettunen of OUSPG.
- [$1000] [171951] High CVE-2013-0880: Use-after-free in database handling. Credit to Chamal de Silva.
- [$500] [167069] Medium CVE-2013-0881: Bad read in Matroska handling. Credit to Atte Kettunen of OUSPG.
- [$500] [165432] High CVE-2013-0882: Bad memory access with excessive SVG parameters. Credit to Renata Hodovan.
- [$500] [142169] Medium CVE-2013-0883: Bad read in Skia. Credit to Atte Kettunen of OUSPG.
- [172984] Low CVE-2013-0884: Inappropriate load of NaCl. Credit to Google Chrome Security Team (Chris Evans).
- [172369] Medium CVE-2013-0885: Too many API permissions granted to web store.
- [Mac only] [171569] Medium CVE-2013-0886: Incorrect NaCl signal handling. Credit to Mark Seaborn of the Chromium development community.
- [171065] [170836] Low CVE-2013-0887: Developer tools process has too many permissions and places too much trust in the connected server.
- [170666] b>Medium CVE-2013-0888: Out-of-bounds read in Skia. Credit to Google Chrome Security Team (Inferno).
- [170569] Low CVE-2013-0889: Tighten user gesture check for dangerous file downloads.
- [169973] [169966] High CVE-2013-0890: Memory safety issues across the IPC layer. Credit to Google Chrome Security Team (Chris Evans).
- [169685] High CVE-2013-0891: Integer overflow in blob handling. Credit to Google Chrome Security Team (Jüri Aedla).
- [169295] [168710] [166493] [165836] [165747] [164958] [164946] Medium CVE-2013-0892: Lower severity issues across the IPC layer. Credit to Google Chrome Security Team (Chris Evans).
- [168570] Medium CVE-2013-0893: Race condition in media handling. Credit to Andrew Scherkus of the Chromium development community.



















